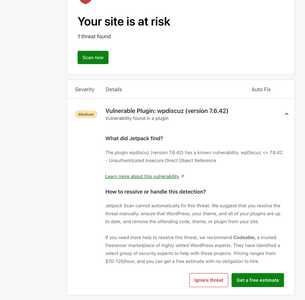
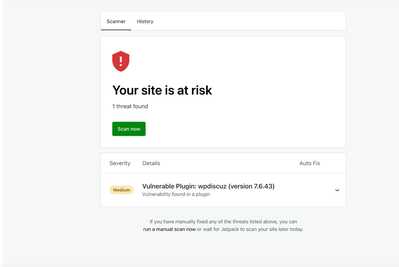
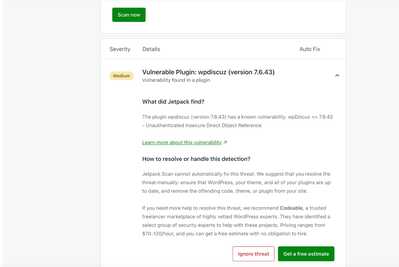
We are facing vulnerable issues. Could you please help us resolve them? We have shared the screenshots for your reference
Hi @prabakaran,
Thank you for contacting us. We'll check and get back to you ASAP.
In case you want to say thank you! 🙂
We'd really appreciate if you leave a good review on the plugin page.
This is the best way to say thank you to this project and the support team.
Please, we hope this issue will be resolved soon.
Hi @Asti,
I second what @prabakaran reported. Wordfence flagged a vulnerability within the latest version of your plugin, V7.6.42.
Details:
1. Wordfence Screenshot: https://prnt.sc/nHIPb3vZtPWz
2. Wordfence Central: https://www.wordfence.com/threat-intel/vulnerabilities/wordpress-plugins/wpdiscuz/wpdiscuz-7642-unauthenticated-insecure-direct-object-reference
Also, the above was reported by another user one week ago as noted here: https://wordpress.org/support/topic/vulnerability-164/
Patch needed ASAP.
Thank you!
Bumping this to add on that it was also flagged by JetPack
Hi @hashtag ,
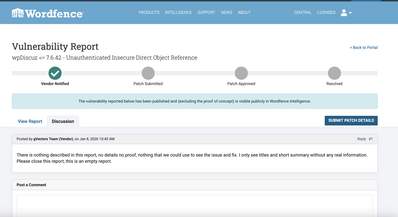
Bumping will not help in this case. At the moment, we are simply waiting for more details. This vulnerability report is essentially empty, it contains no technical details and no proof of concept. With no information provided, we are unable to reproduce, detect, or fix the issue.
We have already fixed dozens of verified reports and released updates for wpDiscuz, but this one is unusual. The reporter only provided a vulnerability type and a title, and nothing else. Based on this, we even suspect that this may be a false positive. The reported risk level is not high (5.3), and no one has contacted us with any supporting details.
We have contacted Wordfence to clarify what this report is about and why they believe this vulnerability exists. So far, no technical explanation has been provided.
In short, this appears to be an unproven, likely false-positive report that was published accidentally. However, if anyone provides concrete details or a valid proof of concept, we will investigate and fix the issue immediately. At this moment, we only have a vague title and claims without evidence. Even Wordfence does not provide any technical details, yet the report is being distributed to websites without proper verification. They also have not responded to our questions on their website.
So we're waiting for details, otherwise this is a report about nothing!
This is not a false positive. The vulnerability is a classic IDOR in wpDiscuz AJAX actions exposed via admin-ajax.php. Below is a minimal proof of concept that worked on a default wpDiscuz installation without any custom modifications, prior to backend hardening.
Affected endpoint:
POST /wp-admin/admin-ajax.php
Example PoC (unauthenticated, no nonce):
curl -X POST https://example.com/wp-admin/admin-ajax.php \
-d "action=wpdVoteOnComment&commentId=1"
Observed behavior (pre-fix): Request is accepted without authentication No nonce validation is enforced
commentId is trusted directly from user input The action is executed or reaches application logic
This allows: Enumeration of commentId values
Mass voting / interaction with arbitrary comments
Bypassing frontend protections (CAPTCHA, rate limits, JS checks)
Abuse via direct HTTP requests without using the wpDiscuz UI
This is a textbook Insecure Direct Object Reference (IDOR) user-controlled object IDs are processed without authorization or ownership checks.
CAPTCHA and per-user limits are frontend-only and are bypassed entirely
High-traffic sites cannot distinguish this abuse from normal AJAX traffic
The issue is not theoretical — it is trivially exploitable with curl or any HTTP client
Mitigation (temporary, user-side): We mitigated this by enforcing backend validation:
Verifying nonce presence for sensitive wpd* actions
Validating that commentId / parentId / replyTo reference existing objects
This confirms the vulnerability exists at the application logic level.
If you need additional PoCs (e.g. subscription abuse, reply manipulation, or request logs), I can provide them. This report is not “about nothing” — it is about missing authorization checks on user-controlled object references.
Thank you for providing the detailed.
We acknowledge the IDOR vulnerability you've described regarding the AJAX endpoint handling. You're correct that the action accepts direct requests without proper authorization checks, which could allow manipulation of comment interactions.
While we take all security reports seriously, we want to provide context on the actual risk level:
- The maximum impact of this vulnerability is manipulation of comment vote counts and potentially comment interactions
- No sensitive data exposure, privilege escalation, or authentication bypass is possible
- No user accounts, personal information, or site content can be compromised
- The CVSS score of 5.3 reflects a Medium severity rating
This aligns with the vulnerability classification it's a valid issue that needs addressing, but not a critical security emergency requiring immediate site-wide patches.
We are actively working on implementing proper authorization checks including:
- Nonce verification for all sensitive AJAX actions
- Backend validation of user permissions
- Verification that comment IDs reference legitimate objects
- Rate limiting at the application level
We'll be releasing an update to address this in our next security release. We'll keep this thread updated on our progress and notify you when the patch is available.
I am impressed with your finding, example given, and solution. Thank you for your detailed contribution. We need more individuals like you in the WordPress universe.
Let's hope the developers at WPDiscuz will take of the vulnerability soon. Your input has proven helpful.
Cheers!
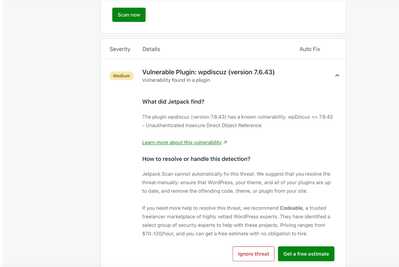
Please update the wpDiscuz to the latest version (v7.6.43) and check if the issue persists.
In case you want to say thank you! 🙂
We'd really appreciate if you leave a good review on the plugin page.
This is the best way to say thank you to this project and the support team.
@skkk Hopefully their update solves this issue in your testing?
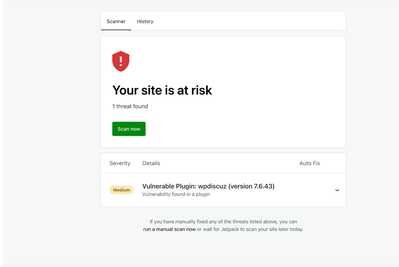
@asti Hi, we have updated to the latest version (v7.6.43), but the issue still persists. I have shared the screenshot from the Jetpack report.
we have updated to the latest version (v7.6.43), but the issue still persists. I have shared the screenshots from the Jetpack report.
@tomson Hey there! Since you pushed the patch, are we waiting on WordFence to approve the patch in terms of it fixing the issue? (So it will stop flagging the plugin, trickling on down to things like JetPack?)
Hi @hashtag, @prabakaran, @skkk and @aerostar
The 7.6.44 version is approved by the problem reporter, the security issue is fixed.